A More Secure Remote Desktop Solution with HopToDesk
Online privacy and security should always be a top priority, especially when it involves sensitive information. Last week, Global Encryption Day reminded us to think more about security. Many remote desktop apps support some kind of encryption to protect data transmitted during remote desktop sessions or file transfers, but what kind of encryption do they offer and how secure are they really?
Risks of Encryption in Transit
Many remote desktop apps that provide encryption only support encryption in transit without end-to-end encryption. This is how most Internet traffic is protected today. For remote desktop apps, data shared between your computers and remote devices may first travel through the Internet to a relay server - a server in between you and the remote session peer usually provided by the remote desktop software provider. Once the traffic reaches the relay server, the remote desktop operator could possibly decrypt and log any peer session data depending on the encryption method used, which could be used to monitor your behavior, target you with ads, detect personal vs commercial usage, or even modify your traffic before it is re-encrypted and sent onwards to the remote session partner. This is quite a downside of relying merely on encryption in transit without end-to-end encryption.
End-To-End Encryption to the Rescue
Popular messaging apps such as WhatsApp, Telegram, and Signal are often touted as more secure than other communications apps due to their use of end-to-end encryption. When implemented correctly, no relay provider or intermediary is able to decrypt user's traffic and data. This is due to the nature of how end-to-end encryption works - the keys to encrypt/decrypt communications data are generated and remain securely with the end users or peers and never shared with the service providers, thus preventing their ability to monitor their user's private data even if they wanted to. This makes end-to-end encryption a strong and preferred method for protecting communications.
Remote Desktop Security Codes - An Industry First
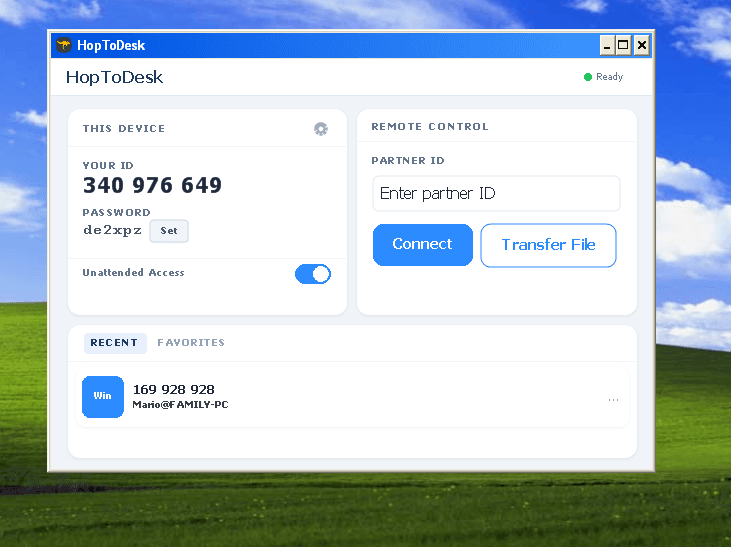
How does one confirm that end-to-end encryption is working and truly secure? The answer is the use of security codes, also known as safety numbers which are often represented by a series of short numbers. Security codes are generated from the end-to-end encryption keys, and not sent between peers. If the end-to-end encrypted session is secure, the security codes will be exactly the same for each of the two connected peers. During a remote session with HopToDesk desktop versions, both peers can view the security code: the controller (the one who starts the session) can click the lock icon at the top right of the connection window while viewing the remote desktop, and the receiver (the user on the remote computer) can view the security code in the small session window at the top right of the screen. While researching the encryption for other remote desktop products, it appears that HopToDesk is likely the first free and open source remote desktop solution that provides the "security code" feature vital to making the most out of end-to-end encryption.
Tell us what you think of the HopToDesk security code feature or other features you wish to see in the future, give HopToDesk a try today.